Today teams are more dispersed than ever before, and this means we are more susceptible to threats and attacks on our systems.
INNOVATE, a Microsoft Gold Partner can help your teams to collaborate in the cloud and online safely, using out multi-layered approach against the threats to your business.
TOP 9 THREATS YOU NEED TO LOOK OUT FOR IN YOUR BUSINESS
As the last year or so has shown, cyber-attacks are on the rise and becoming increasingly more complex than ever before. It is vital that not only do you protect your data and identities but also that you are aware of the types of threats that exist.
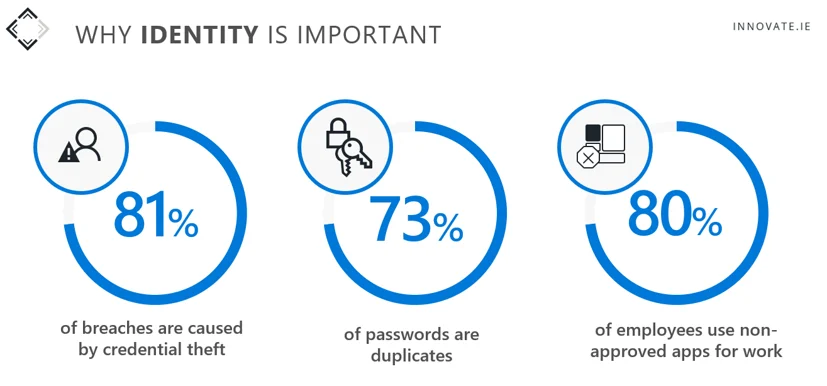
- Compromised Credentials
One of the biggest issues we see are weak or shared user credentials and passwords.
- Malicious Code
This method is less popular now as it provides less return for the hackers, but it is software that destroys files commonly known as a virus or a worm.
- Ransomware (e.g. WannaCry)
Ransomware is where the system has been encrypted by hackers and they will demand money in return for a key to decrypt the system. The most recent example of this has been with the HSE cyber-attack by hackers using Conti ransomware.
- Social Engineering
This is where hackers manipulate people in businesses into providing information or performing actions which will give them access to sensitive information or monetary gains. An example is CFO Fraud – where employees are duped by a very convincing email to transfer funds to a bank account.
- Phishing
A social engineering attack used to steal user data & credentials by duping the user into opening an email or message or clicking on a link.
- Spoofing
The hacker acts like a legitimate business or contact to obtain user data & credentials.
- Access Through Intermediaries
If your customers, suppliers or anyone who interacts with your business do not have their systems protected properly you can be exposed to threats also.
- Brute Force Attack
Very rarely used now, but the hacker makes continued attempts at guessing username and password details to gain access. Distributed Denial of Service (DDoS)
This is where a hacker will use bots to send a large amount of traffic to a site or server to bring it down. This is more of an inconvenience than causing any damage. Recently, several smaller ISP’s servers were subject to a DDoS attack.
OUR APPROACH
In the past, we focussed on the edge of the network to protect us by implementing a firewall, – now we have to think about location, devices, users, applications and data. As we all move to online collaboration tools like Microsoft Teams and working in the cloud, we need to adopt a multi-layered security approach.

How Microsoft can protect your business:
- Multi Factor Authentication is an additional security layer for your business and can help your employees identify themselves to strengthen your defence against hacking and attacks.
- As BYOD becomes more popular, organistaion incur the risk that personal devices might bring security vulnerabilities and exploits with them when employees and other users connect to the cloud. Utilising Azure Active Directory (Azure AD) in tandem with Microsoft InTune to implement conditional access will provide you with the necessary tools to protect your employee’s identity and in turn your business.
- Threat Protection with Microsoft InTune allows you to set policies centrally and have greater control over the devices in your network. It also allows you to wipe devices of company data if they do go missing
- Conditional Access helps to ensure that access to company data or applications is only granted after Microsoft validates device health and compliance status, in addition to authorised user credentials.
- Windows Virtual Desktop provides secure remote working providing the familiarity and compatibility of Windows 10 giving access through the Cloud to legacy applications, as well as increasing the amount of storage space you have.
KEY TAKEAWAYS
- Keep all employees informed and maintain guidelines on safe practices
- Try not to run the business on outdated applications and operating systems, as they are more prone to infiltration
- Use a scalable and centrally managed anti-malware solution and make sure it is regularly updated
- Have a thought-out password policy and we strongly recommend using two-factor authentication for all critical processes
- Layer your security solutions to give you the best possible protection
- Backup! Backup! Backup! Secure backup and recovery can prevent many headaches in the case of ransomware infections and other attempts to jeopardise your data
If you would like to learn more about protecting your business from threats with one of our specialists, please feel free to contact us at:
- Email: ask@innovate.ie
- Phone: +353 (1) 215 3999
If you are not quite ready to get in touch and would like to read more details, take a look at our webinar on “Getting the most from Microsoft”:



